How to Block Access to All Data for Guest Users
Your application can use the Backendless API to access data, run searches, and store, update and delete objects in the database. When users authenticate themselves with the backend, all subsequent API calls are executed on the behalf of the logged-in user.
However, if an API call is made without an authenticated user in the session, it is associated with an anonymous user. As a result, in an application that does not restrict data access, the data is exposed to everyone.
Restricting access for anonymous (non-authenticated) users is a very straight-forward process. You have multiple options ranging from denying access globally for all API calls to setting restrictions at the data table level or even at the individual object level. In this article, we will review the process for restricting access globally.
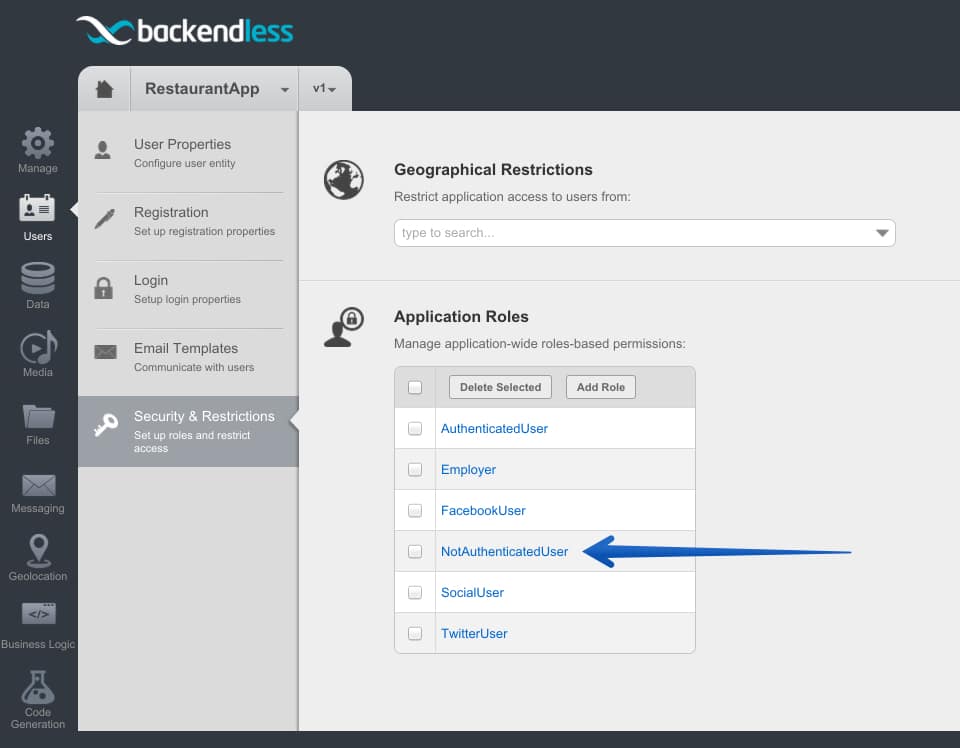
When an application makes an API call by a “guest” user, meaning a user who has not logged in, Backendless associates the user in that session with the NotAuthenticatedUser role. It is a built-in (or system) role and every Backendless application automatically includes it. You can see that role in the Applications Roles section located in the Users > Security & Restrictions screen of Backendless Console.
When you click the NotAuthenticatedUser role, the Console displays the global security role matrix. To disable access for all operations for the non-authenticated users, click every green checkmark until the screen looks as shown below:
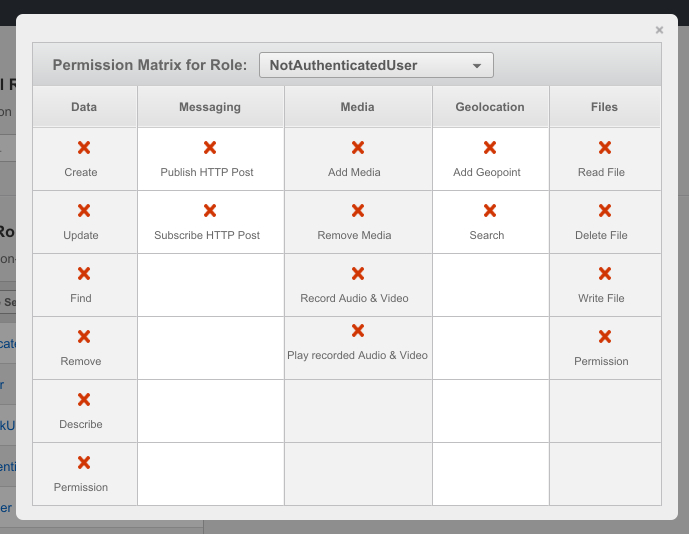
As a result of the changes described above, all API operations made by anonymous users will be rejected by Backendless. It is that easy.
Enjoy!